Free Security+ Practice Test: 1,812 SY0-701 Questions (2026)
Take a free Security+ practice test with 1,812 SY0-701 questions. Includes 25 sample questions with answers, AI explanations, and a gamified RPG battle system. Start practicing now.
Builder of SecuSpark. 24 shipped projects across healthcare, defense, and education. Built this platform because textbooks never worked for my ADHD brain — so I turned exam prep into an RPG. @PawelBuilds
Table of Contents
Looking for a free Security+ practice test? You are in the right place. SecuSpark has 1,812 SY0-701 practice questions covering all five exam domains — and you can start practicing right now without creating an account. Below you will find 25 sample questions to test yourself immediately, plus a breakdown of why gamified practice tests produce better exam scores than static question banks.
The CompTIA Security+ SY0-701 exam requires a passing score of 750 out of 900 and tests you across five domains: General Security Concepts, Threats and Vulnerabilities, Security Architecture, Security Operations, and Security Program Management. Most candidates need between 500 and 1,500 practice questions to pass confidently. The 25 questions below give you a realistic preview of what to expect.
25 Free Security+ SY0-701 Sample Questions
These 25 questions span all five SY0-701 domains. Each question has four options and the correct answer revealed below it. Use them as a quick diagnostic — if you score below 60%, you have significant gaps to address before exam day.
Domain 1: General Security Concepts (Questions 1-5)
Question 1. A company implements a policy requiring employees to use smart cards combined with a PIN to access the server room. Which security concept does this BEST demonstrate?
- Least privilege
- Multifactor authentication
- Role-based access control
- Single sign-on
Answer: B. Multifactor authentication combines something you have (smart card) with something you know (PIN). These are two distinct authentication factor categories.
Question 2. An organization wants to ensure that sensitive documents cannot be copied to USB drives. Which security control type is being implemented?
- Detective
- Corrective
- Preventive
- Compensating
Answer: C. Blocking USB drive usage is a preventive control — it stops the unauthorized action before it occurs. Detective controls identify events after the fact; corrective controls fix them.
Question 3. Which of the following BEST describes the concept of non-repudiation?
- Ensuring data has not been modified in transit
- Guaranteeing a sender cannot deny having sent a message
- Verifying a user's identity before granting access
- Encrypting data so only the intended recipient can read it
Answer: B. Non-repudiation prevents a party from denying an action they performed, typically achieved through digital signatures. Integrity (A), authentication (C), and confidentiality (D) are related but distinct concepts.
Question 4. A security administrator is implementing a zero trust architecture. Which principle is MOST fundamental to this approach?
- All internal network traffic is trusted by default
- Never trust, always verify — regardless of network location
- Perimeter firewalls are sufficient to protect internal assets
- VPN connections grant full access to all internal resources
Answer: B. Zero trust assumes no implicit trust based on network location. Every access request must be authenticated, authorized, and encrypted — whether it originates inside or outside the corporate network.
Question 5. Which of the following describes the gap analysis process in security?
- Identifying the difference between current security posture and desired security state
- Scanning for open ports on a network
- Testing an application for SQL injection vulnerabilities
- Monitoring network traffic for anomalies
Answer: A. A gap analysis compares an organization's current security controls against a target framework or standard (e.g., NIST, ISO 27001) to identify where improvements are needed.
Domain 2: Threats, Vulnerabilities, and Mitigations (Questions 6-10)
Question 6. An employee receives an email that appears to be from the CEO requesting an urgent wire transfer. The email address uses a domain that is one letter different from the company's actual domain. What type of attack is this?
- Vishing
- Whaling
- Smishing
- Pharming
Answer: B. Whaling is a spear-phishing attack specifically targeting high-level executives or impersonating them. The lookalike domain is a common whaling technique called typosquatting.
Question 7. A security analyst discovers that attackers are exploiting a vulnerability in a web application that the vendor has not yet released a patch for. What type of vulnerability is this?
- Legacy vulnerability
- Zero-day vulnerability
- Default configuration vulnerability
- Backdoor vulnerability
Answer: B. A zero-day vulnerability is one that is actively exploited before the vendor is aware of it or has released a fix. The term "zero-day" refers to the vendor having zero days to address the issue.
Question 8. Which type of malware specifically encrypts files and demands payment for the decryption key?
- Trojan
- Rootkit
- Ransomware
- Keylogger
Answer: C. Ransomware encrypts the victim's data and demands a ransom payment (usually in cryptocurrency) in exchange for the decryption key. Trojans disguise themselves as legitimate software, rootkits hide their presence, and keyloggers record keystrokes.
Question 9. An attacker sets up a rogue wireless access point with the same SSID as the corporate Wi-Fi network. Employees unknowingly connect to it. What is this attack called?
- Bluesnarfing
- Evil twin
- Replay attack
- ARP poisoning
Answer: B. An evil twin attack uses a rogue access point that mimics a legitimate network's SSID. Victims connect to the attacker's AP, allowing the attacker to intercept traffic in a man-in-the-middle position.
Question 10. During a penetration test, the tester discovers that a web application is vulnerable to an attack where user input is reflected back in the browser without sanitization. Which vulnerability is this?
- SQL injection
- Cross-site scripting (XSS)
- Cross-site request forgery (CSRF)
- Directory traversal
Answer: B. Cross-site scripting (XSS) occurs when an application includes unvalidated user input in its output. Reflected XSS specifically bounces user input back in the server response without proper sanitization.
Domain 3: Security Architecture (Questions 11-15)
Question 11. A company wants to isolate its public-facing web servers from its internal network while still allowing controlled communication between them. Which network architecture should be implemented?
- Virtual private network (VPN)
- Demilitarized zone (DMZ)
- Network address translation (NAT)
- Software-defined networking (SDN)
Answer: B. A DMZ is a perimeter network segment that sits between the public internet and the internal network. It allows hosting public-facing services while protecting internal resources through firewall rules on both sides.
Question 12. Which cloud service model provides the customer with the MOST control over the underlying infrastructure?
- Software as a Service (SaaS)
- Platform as a Service (PaaS)
- Infrastructure as a Service (IaaS)
- Function as a Service (FaaS)
Answer: C. IaaS gives customers control over virtual machines, storage, and networking. The cloud provider manages the physical hardware. PaaS adds OS/runtime management by the provider, and SaaS manages everything except data and user access.
Question 13. A security architect recommends deploying a web application firewall (WAF) in front of the organization's e-commerce platform. What is the PRIMARY purpose of this control?
- To encrypt data in transit between the server and client
- To filter and monitor HTTP traffic for application-layer attacks
- To load balance traffic across multiple web servers
- To prevent DDoS attacks at the network layer
Answer: B. A WAF inspects HTTP/HTTPS traffic and blocks requests that match attack signatures like SQL injection, XSS, and other OWASP Top 10 threats. While it may offer some DDoS mitigation, its primary role is application-layer protection.
Question 14. An organization is deploying infrastructure using code templates that can be version-controlled and reproduced identically across environments. Which concept does this BEST describe?
- Containerization
- Infrastructure as Code (IaC)
- Microservices architecture
- Serverless computing
Answer: B. Infrastructure as Code (IaC) uses machine-readable definition files (e.g., Terraform, CloudFormation) to provision and manage infrastructure. This enables version control, reproducibility, and consistent deployments.
Question 15. Which of the following is an advantage of using hardware security modules (HSMs) for key management?
- HSMs are less expensive than software-based key storage
- HSMs provide tamper-resistant storage for cryptographic keys
- HSMs eliminate the need for key rotation policies
- HSMs automatically encrypt all data at rest on the network
Answer: B. HSMs are dedicated hardware devices designed to generate, store, and manage cryptographic keys in a tamper-resistant environment. They protect keys from extraction even if the host system is compromised.
Domain 4: Security Operations (Questions 16-20)
Question 16. A SIEM system generates an alert for unusual outbound data transfers occurring at 3 AM from a database server. What should be the analyst's FIRST action?
- Immediately shut down the database server
- Validate the alert and determine if it is a true positive
- Contact law enforcement
- Begin forensic imaging of the server
Answer: B. The first step in incident response triage is to validate the alert. Many SIEM alerts are false positives. Before taking disruptive action like shutting down a server, the analyst should confirm the alert represents a real threat.
Question 17. Which log source would be MOST useful for investigating a suspected brute-force attack against a Windows domain controller?
- Web server access logs
- Windows Security event logs
- DNS query logs
- DHCP lease logs
Answer: B. Windows Security event logs (specifically Event IDs 4625 for failed logons and 4624 for successful logons) provide the authentication data needed to identify brute-force patterns against Active Directory.
Question 18. During a vulnerability scan, multiple systems are flagged for missing critical patches. The security team cannot immediately patch all systems due to production uptime requirements. Which approach is MOST appropriate?
- Ignore the vulnerabilities until the next maintenance window
- Prioritize patching based on risk assessment and apply compensating controls to high-risk systems
- Immediately patch all systems regardless of production impact
- Disable the vulnerability scanner to reduce alert fatigue
Answer: B. Risk-based prioritization balances security with business continuity. High-risk vulnerabilities on internet-facing systems get patched first, while compensating controls (IPS rules, network segmentation) mitigate risk until remaining systems can be patched.
Question 19. A company requires that all hard drives from decommissioned laptops be completely unrecoverable. Which data destruction method is MOST appropriate?
- Quick format
- Degaussing
- Physical shredding
- File deletion
Answer: C. Physical shredding is the most thorough data destruction method and renders data completely unrecoverable. Degaussing works for magnetic media but not SSDs. Quick format and file deletion leave data recoverable with forensic tools.
Question 20. A security analyst is reviewing firewall logs and notices repeated connection attempts from the same external IP to sequential port numbers on a server. What is this activity MOST likely?
- Denial-of-service attack
- Port scanning
- Man-in-the-middle attack
- DNS tunneling
Answer: B. Sequential connection attempts across port numbers is the signature pattern of a port scan. Attackers use port scanning to enumerate open services on a target system during the reconnaissance phase.
Domain 5: Security Program Management and Oversight (Questions 21-25)
Question 21. An organization must comply with a regulation that requires personally identifiable information (PII) to be encrypted both in transit and at rest. Which compliance framework is MOST likely driving this requirement?
- PCI DSS
- GDPR
- SOX
- HIPAA
Answer: B. The GDPR (General Data Protection Regulation) specifically mandates the protection of PII for EU citizens and recommends encryption as a technical safeguard. While PCI DSS requires encryption of cardholder data and HIPAA covers health records, GDPR has the broadest PII protection scope.
Question 22. A risk assessment identifies a potential threat with a likelihood rating of "Medium" and an impact rating of "High." Using a qualitative risk matrix, how should this risk be categorized?
- Low risk
- Medium risk
- High risk
- Critical risk
Answer: C. In a standard qualitative risk matrix, Medium likelihood combined with High impact typically results in a High risk rating. This combination warrants active risk treatment (mitigation, transfer, or avoidance).
Question 23. Which of the following BEST describes the purpose of a Business Impact Analysis (BIA)?
- To identify all vulnerabilities in an organization's systems
- To determine the effect of disruption on critical business functions and establish recovery priorities
- To test the organization's incident response plan
- To audit compliance with regulatory requirements
Answer: B. A BIA identifies critical business processes, quantifies the impact of their disruption (in terms of revenue, operations, and reputation), and establishes recovery time objectives (RTOs) and recovery point objectives (RPOs).
Question 24. An organization decides to purchase cyber insurance to address the financial impact of a potential data breach. Which risk management strategy is this?
- Risk avoidance
- Risk mitigation
- Risk transfer
- Risk acceptance
Answer: C. Purchasing insurance is the classic example of risk transfer — the financial burden of the risk is shifted to a third party (the insurer). The organization still owns the risk but transfers the financial consequences.
Question 25. During a third-party vendor assessment, a security team discovers the vendor does not have a SOC 2 Type II report. What does this finding indicate?
- The vendor has not been audited for security, availability, and confidentiality controls over a period of time
- The vendor's software has not been penetration tested
- The vendor does not encrypt data in transit
- The vendor is not compliant with GDPR
Answer: A. A SOC 2 Type II report provides an independent auditor's assessment of a service organization's controls over a sustained period (typically 6-12 months). Its absence means there is no third-party assurance that the vendor's security controls are operating effectively over time.
How did you score?
20-25 correct: You are in strong shape — focus on weak domains. 15-19 correct: Solid foundation but gaps to fill. 10-14 correct: Significant study needed. Below 10: Start with a structured study plan before heavy practice testing. These 25 questions are just a sample — the full 1,812-question bank covers every SY0-701 objective in depth.
Why Gamified Practice Tests Work Better
Traditional practice tests follow a loop: read question, pick answer, see explanation, repeat. It works, but it is boring — and boredom is the top reason candidates abandon their study plans before exam day. Research on active recall and spaced repetition shows that engagement directly correlates with retention. The more actively your brain processes information, the stronger the memory trace.
SecuSpark replaces the standard quiz loop with an RPG battle system. Every question is an attack in a fight against an enemy. Answer correctly to deal damage. Answer wrong and you take a hit. Your character has HP, you earn XP, you level up through 100 levels, and your character visually evolves through 30 stages as you progress.
Every Security+ question is a battle. Answer correctly to attack the enemy. Answer wrong and you take damage.
This is not a gimmick. The battle system exploits three proven learning mechanisms:
- Active recall under stakes: Your character's HP creates artificial consequences for wrong answers. Your brain treats this as meaningful stakes, increasing attention and encoding depth.
- Variable reward schedules: XP, loot drops, critical hits, and character evolution provide unpredictable rewards — the same mechanism that makes games addictive, redirected toward learning.
- Progress visualization: Watching your character evolve from a Level 1 slime to a Level 30 elemental form provides tangible evidence of your study progress beyond just "82% accuracy."
The campaign mode maps directly to SY0-701 exam objectives. There are 133 campaign nodes, 19 domain bosses, and 12 final bosses across the full certification path. Each domain boss tests a specific Security+ domain, so completing the campaign means you have covered every exam objective at least once.
AI Explanations That Actually Teach
Getting a question wrong is only useful if you understand why you got it wrong. Static explanations repeat the same text whether you picked A or D. SecuSpark uses GPT-4o-mini to generate dynamic explanations that address your specific wrong answer.
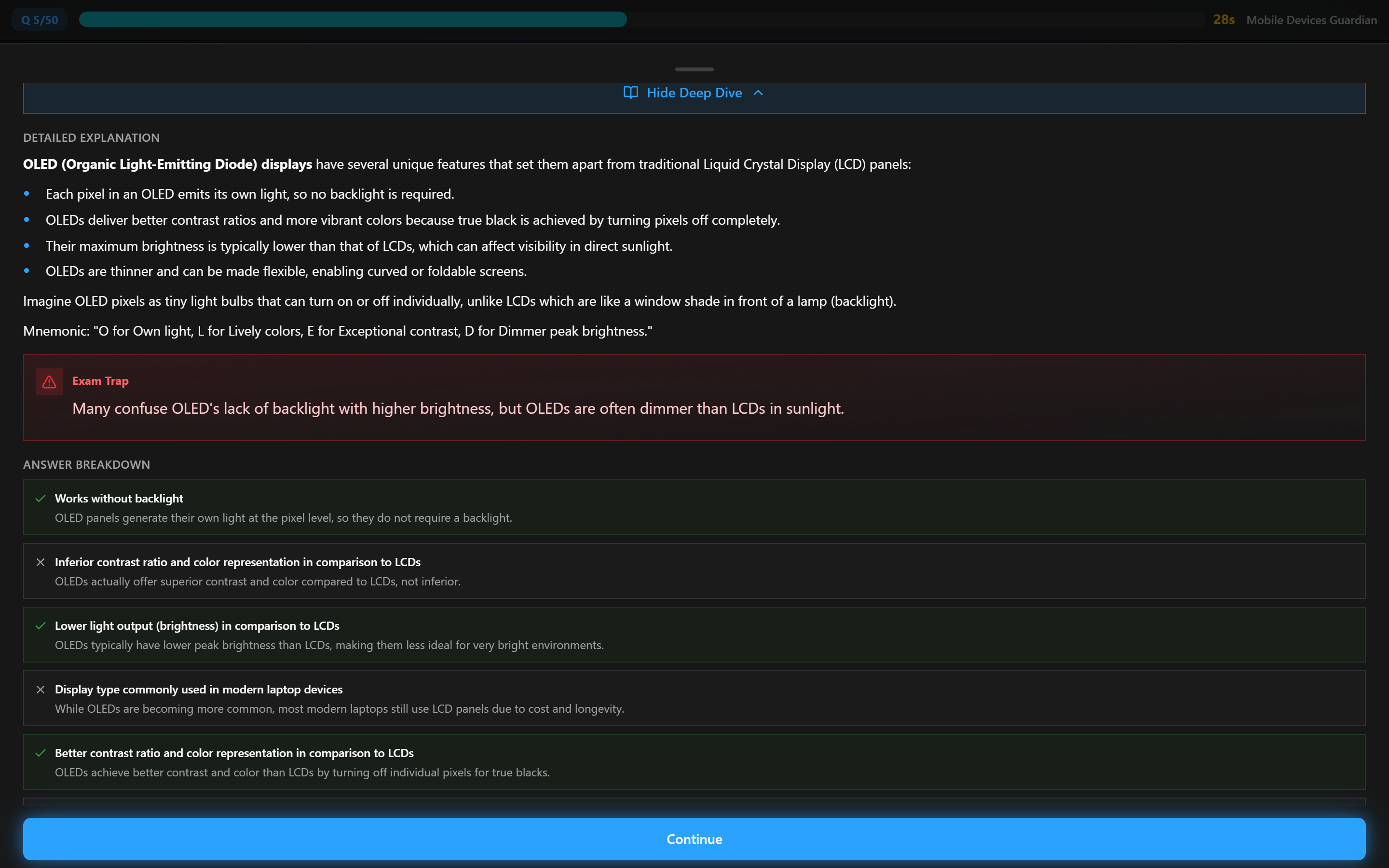
When you answer incorrectly, the AI explains exactly why your choice was wrong and breaks down the correct answer.
The AI provides:
- Targeted explanations — addresses why your specific wrong answer was tempting and why it fails
- Memory mnemonics — custom memory aids like "CIA triad: See It Always"
- Real-world analogies — connects abstract concepts to everyday scenarios
- Exam objective mapping — tells you exactly which SY0-701 domain and sub-objective a question covers
The AI tutor goes deeper than standard explanations — ask follow-up questions until the concept clicks.
This is the difference between "the answer is B" and actually understanding why B is correct and why your reasoning about A was flawed. Over 1,812 questions, that difference compounds into significantly deeper comprehension of Security+ material.
SecuSpark vs Other Free Security+ Practice Tests
If you are searching for a free Security+ practice test, you have options. Here is how they compare on features that actually matter for passing the exam.
| Feature | SecuSpark | ExamCompass | CertMaster | Flashcard Apps |
|---|---|---|---|---|
| Free Tier | Yes (15 questions/day) | Yes (fully free) | No ($149/cert) | Varies |
| SY0-701 Questions | 1,812 | ~200-300 | ~300-500 | Varies |
| AI Explanations | Yes (GPT-4o-mini) | No | No | No |
| Gamification | RPG battles, XP, 100 levels | None | None | Streaks only |
| PvP Arena | Yes (ELO matchmaking) | No | No | No |
| Spaced Repetition | Built-in flashcards | No | Adaptive only | Yes |
| Progress Tracking | Per-domain analytics | No | Yes | Basic |
| Offline Mode | Yes (works offline) | No | No | Some |
| Multiple Certs | 4 (Sec+, A+, Net+, CySA+) | Multiple | 1 per license | Varies |
| Paid Price | $14.99/mo or $34.99/qtr | Free (ad-supported) | $149/certification | $5-30/mo |
ExamCompass is the most popular free option. It offers solid question volume organized by SY0-701 topic, but the interface is ad-heavy, questions tend to be simpler than the actual exam, and there are zero explanations, zero progress tracking, and zero engagement features. It is a good supplement but not sufficient as your primary study tool.
CertMaster Practice is CompTIA's official tool. Questions are high quality (written by the exam creators), but at $149 per certification with no free tier, it is the most expensive option. No AI, no gamification, no social features. (See our full CertMaster comparison.)
Flashcard apps (Anki, Quizlet, Brainscape) are great for vocabulary and definitions but lack the scenario-based question format that SY0-701 relies on. The exam tests application of knowledge, not memorization — you need practice questions that present realistic scenarios.
What the Security+ SY0-701 Exam Covers
Before diving into practice tests, make sure you understand what the exam expects. The SY0-701 exam has five domains with specific weightings:
| Domain | Weight | Key Topics |
|---|---|---|
| 1.0 General Security Concepts | 12% | CIA triad, zero trust, AAA, gap analysis, security controls |
| 2.0 Threats, Vulnerabilities, and Mitigations | 22% | Malware, social engineering, application attacks, indicators of compromise |
| 3.0 Security Architecture | 18% | Network architecture, cloud security, resilience, encryption, PKI |
| 4.0 Security Operations | 28% | Monitoring, incident response, vulnerability management, automation |
| 5.0 Security Program Management | 20% | Governance, risk management, compliance, auditing, security awareness |
Domain 4 (Security Operations) carries the heaviest weight at 28%. This means you should spend roughly a quarter of your study time on monitoring, incident response, and vulnerability management. SecuSpark's campaign mode allocates questions proportionally to these domain weights, so you naturally spend more time on higher-weighted domains.
The exam also includes performance-based questions (PBQs) that require you to solve a scenario interactively. Practice tests alone cannot fully prepare you for PBQs, but they build the knowledge foundation you need to tackle them confidently. For a full breakdown of what score you need, see our Security+ passing score guide.
How to Use Free Practice Tests Effectively
Taking practice tests without a strategy is like going to the gym without a plan — you will get some results, but far fewer than with a structured approach. Here is how to maximize the value of free Security+ practice questions:
- Diagnostic first. Take a 25-50 question practice test before studying anything. Your score identifies which domains need the most work. Do not study before the diagnostic — you need an honest baseline.
- Study by domain, test by domain. After your diagnostic, tackle your weakest domain first. Study the material, then take practice questions for only that domain. Do not mix domains until each individual domain is above 80% accuracy.
- Read every explanation. Even on questions you answered correctly. Sometimes you got the right answer for the wrong reason. AI explanations are especially valuable here because they can identify flawed reasoning.
- Space your repetitions. Do not cram 200 questions in one session. 30-50 questions per day over several weeks produces far better retention than marathon sessions. SecuSpark's spaced-repetition flashcards automate this timing for you.
- Simulate exam conditions. At least twice before your exam date, take a full-length 90-question timed practice test (90 minutes). This builds stamina and time management skills. SecuSpark offers timed exam mode for this purpose.
The 80/80 rule
You are ready to schedule your Security+ exam when you consistently score above 80% across all five domains on practice tests. Not 80% overall — 80% per domain. One weak domain can sink your exam score even if your average is above the 750/900 passing score.
Beyond Security+: Your Full Certification Path
Security+ is the most popular CompTIA certification and often the first step in a cybersecurity career. Once you pass, you will want to know what comes next. SecuSpark covers the full core path:
- A+ (220-1201): 1,252 practice questions — ideal if you want to backfill hardware and OS fundamentals
- Network+ (N10-009): 1,070 practice questions — strengthens your networking foundation
- CySA+ (CS0-003): 1,785 practice questions — the natural next step after Security+ for security analysts
- PenTest+ (PT0-003): 554 practice questions — offensive security and penetration testing
All five certifications are included in a single subscription. No extra licenses, no per-cert pricing. If Security+ is worth it for your career (and for most IT professionals it is), having CySA+ next in the pipeline gives you a clear path to specialization.
Frequently Asked Questions
Is this practice test really free?
Yes. SecuSpark's free tier gives you 15 practice questions per day with full AI explanations, access to the RPG battle system, flashcards, and PvP arena. No credit card required. The full 1,812-question bank is available on Pro ($14.99/mo or $34.99/qtr), which also covers A+, Network+, CySA+, and PenTest+.
Are these questions updated for the SY0-701 exam?
Yes. All 1,812 Security+ questions in SecuSpark are written for the current SY0-701 exam objectives. The exam was updated from SY0-601 to SY0-701 in November 2023. If you are using any practice test resource, verify that it explicitly states SY0-701 coverage — older SY0-601 questions may cover deprecated topics.
How many practice questions do I need to pass Security+?
Most successful candidates answer between 500 and 1,500 unique practice questions before their exam. The key metric is not question count but per-domain accuracy. Aim for consistent 80%+ accuracy across all five SY0-701 domains. SecuSpark's 1,812 questions are more than sufficient as your primary practice source when combined with instructional content (video courses, study guides).
Can I use this practice test on my phone?
Yes. SecuSpark is a progressive web app that works on any device with a browser — phone, tablet, laptop, or desktop. It also works offline, so you can practice on your commute or anywhere without internet. Just open secuspark.com in your browser and start practicing.
How is this different from ExamCompass?
ExamCompass offers free static quizzes with no explanations, no progress tracking, and no engagement features. SecuSpark adds AI-powered explanations for every question, an RPG battle system that makes studying engaging, PvP matchmaking for competitive practice, spaced-repetition flashcards, and per-domain analytics to identify your weak areas. ExamCompass is a solid free supplement; SecuSpark is a complete study system.
Do I need to create an account?
You can start practicing immediately without an account. SecuSpark stores progress locally in your browser using IndexedDB (offline-first architecture). Creating a free account with email or Google lets you sync your progress across devices and access your stats from anywhere.
What is the RPG battle system?
Every practice question is framed as a battle between your character and an enemy. Correct answers deal damage to the enemy. Wrong answers damage your character. You earn XP, level up through 100 levels, your character visually evolves through 30 stages, and you collect weapons and items. It sounds like a game because it is — but the questions are real Security+ SY0-701 exam material, and the engagement mechanics keep you studying longer than traditional flashcards.
Is 1,812 questions enough to pass Security+?
For most candidates, yes — when combined with instructional content. A bank of 1,812 human-written, scenario-based questions covering all SY0-701 objectives provides thorough coverage. Quality matters more than quantity. SecuSpark's questions include realistic scenarios and four-option multiple choice format matching the actual exam. Supplement with a video course (Professor Messer's free course is excellent) and you have a complete study plan.
Quick win, no signup
Try 5 free Security+ practice questions
No signup required. AI explains every wrong answer so you actually learn.
Stop Reading, Start Practicing
6,400+ practice questions across 5 CompTIA certs. 3 free exams per cert — no signup required. AI explains every wrong answer. Campaign Pass unlocks all exams and the RPG battle campaign.
Free Study Tools
Related Articles
Best CompTIA Security+ Study Materials & Resources (2026)
Best Security+ SY0-701 study materials ranked for 2026. Books, videos, practice tests, and labs compared by effectiveness and cost.
Security+ Study Schedule: 30, 60, 90-Day Plans (SY0-701)
Free Security+ SY0-701 study schedules for 30, 60, and 90 days. Daily domain breakdowns, practice exam checkpoints, and review days built in.
